NSX-T 2.1 GA Installation using ovftool
Update on 23 Dec 2017
NSX-T 2.1 was GA. I thought since Im going to re-do the whole process, I might as well take new screenshots as well.
You might be wondering why would I want to use ovftool to install NSX-T appliances. This is because my management host is not being managed by a vCenter and it failed when using the vSphere Client.
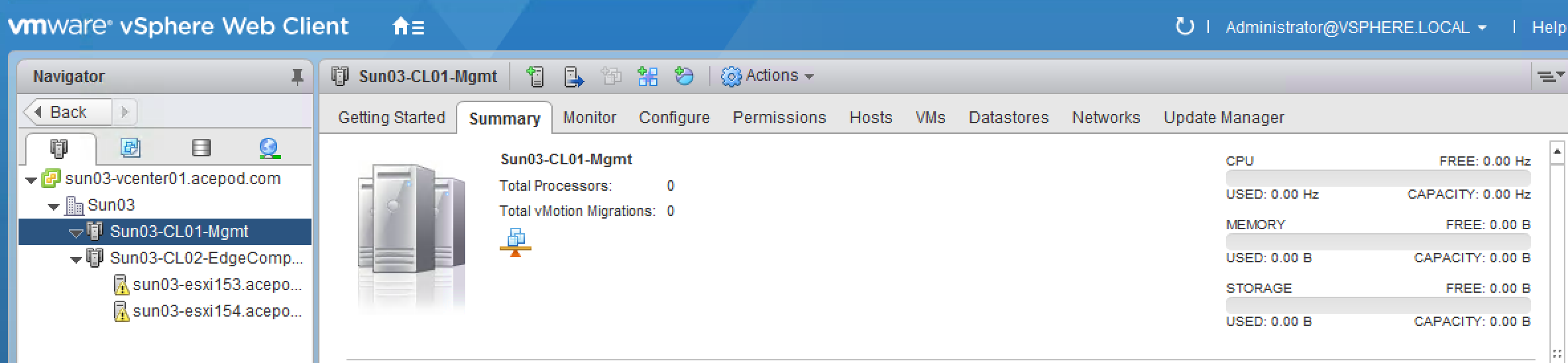
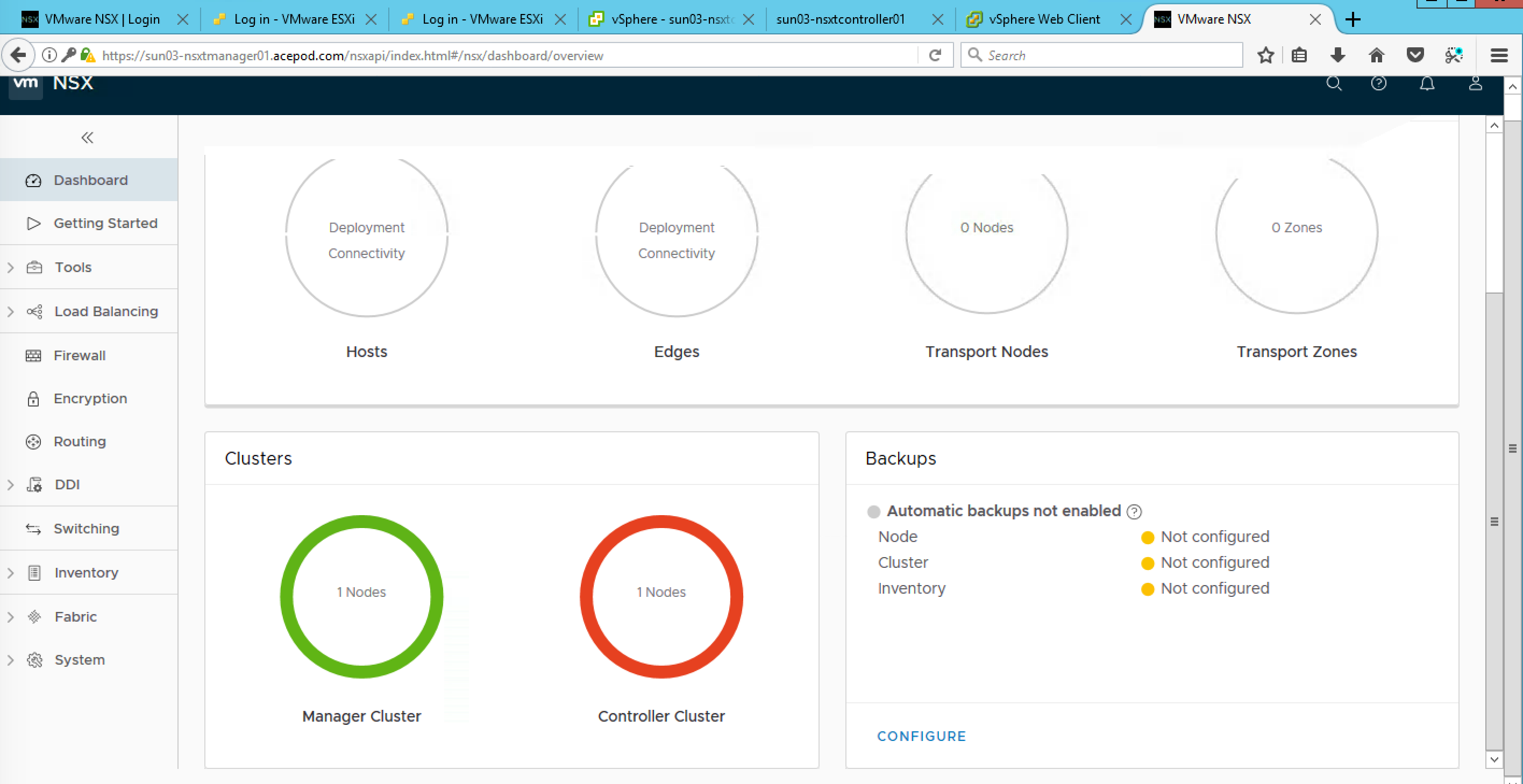
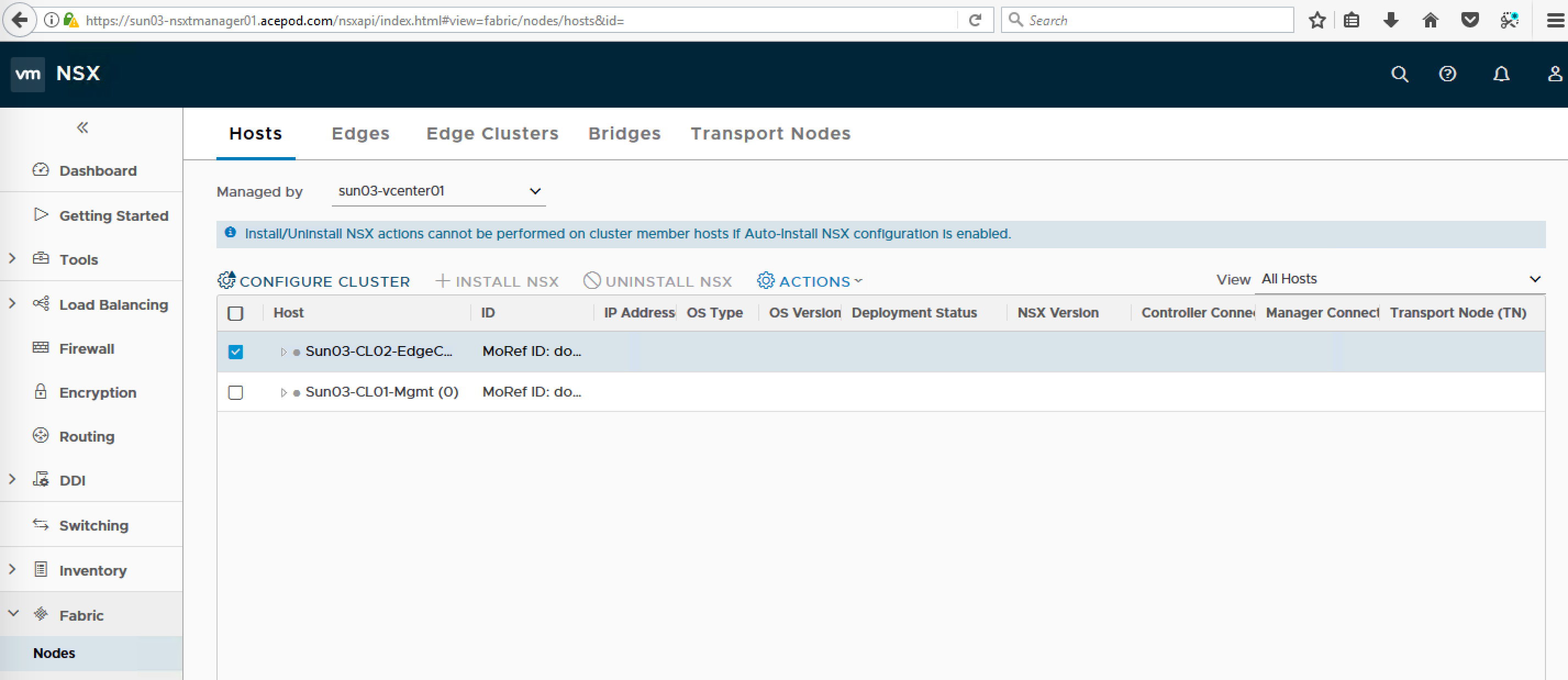
You can see from the screenshot above, I only have hosts for the EdgeComp Cluster. As I do not have additional hosts for the management cluster, I will be using an existing management host that is standalone.
While reading the NSX-T Installation Guide documentation, realize they did mention of using an alternative method ie using the OVF Tool to install the NSX Manager. I reckon, this would be useful for automated install and the other reason, is that NSX-T architecture is to move away from the dependency of vCenter. NSX-T could be deployed in a 100% non-vSphere environment, like for example KVM.
Preparing for Installation
These are the files I will be using for the NSX-T Installation.
1) NSX Manager – nsx-unified-appliance-2.1.0.0.0.7395503.ova
2) NSX Controllers – nsx-controller-2.1.0.0.0.7395493.ova
3) NSX Edges – nsx-edge-2.1.0.0.0.7395503.ova
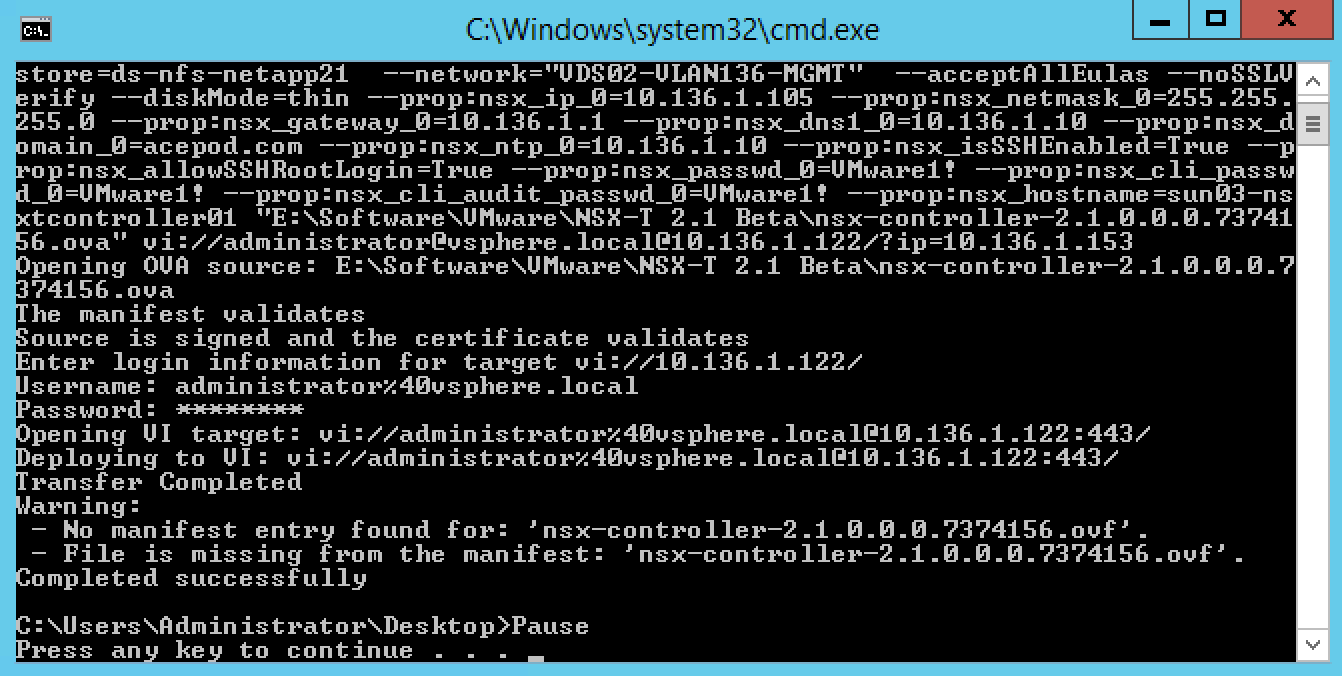
Installing NSX-T Manager using ovftool
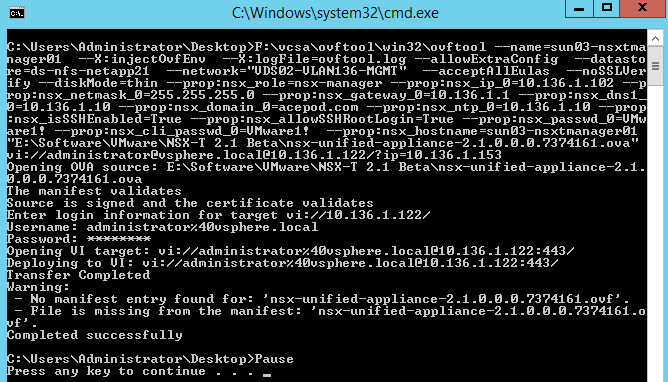
Following the guide, and had to modify the ovftool command. So this is the command I used and I put into a batch file. Maybe later I will incorporate it into the powershell script I used to deploy the vSphere part.
You can find the script here.
The ESXi host Im using is 6.0U2 and it does not takes in the OVF properties. So I had no choice, but to deploy to the vcenter instead and to the EdgeComp hosts.
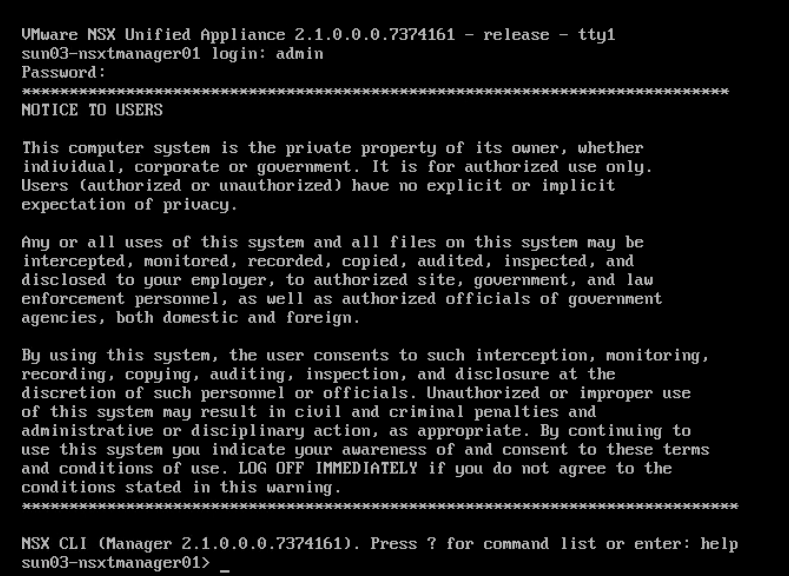
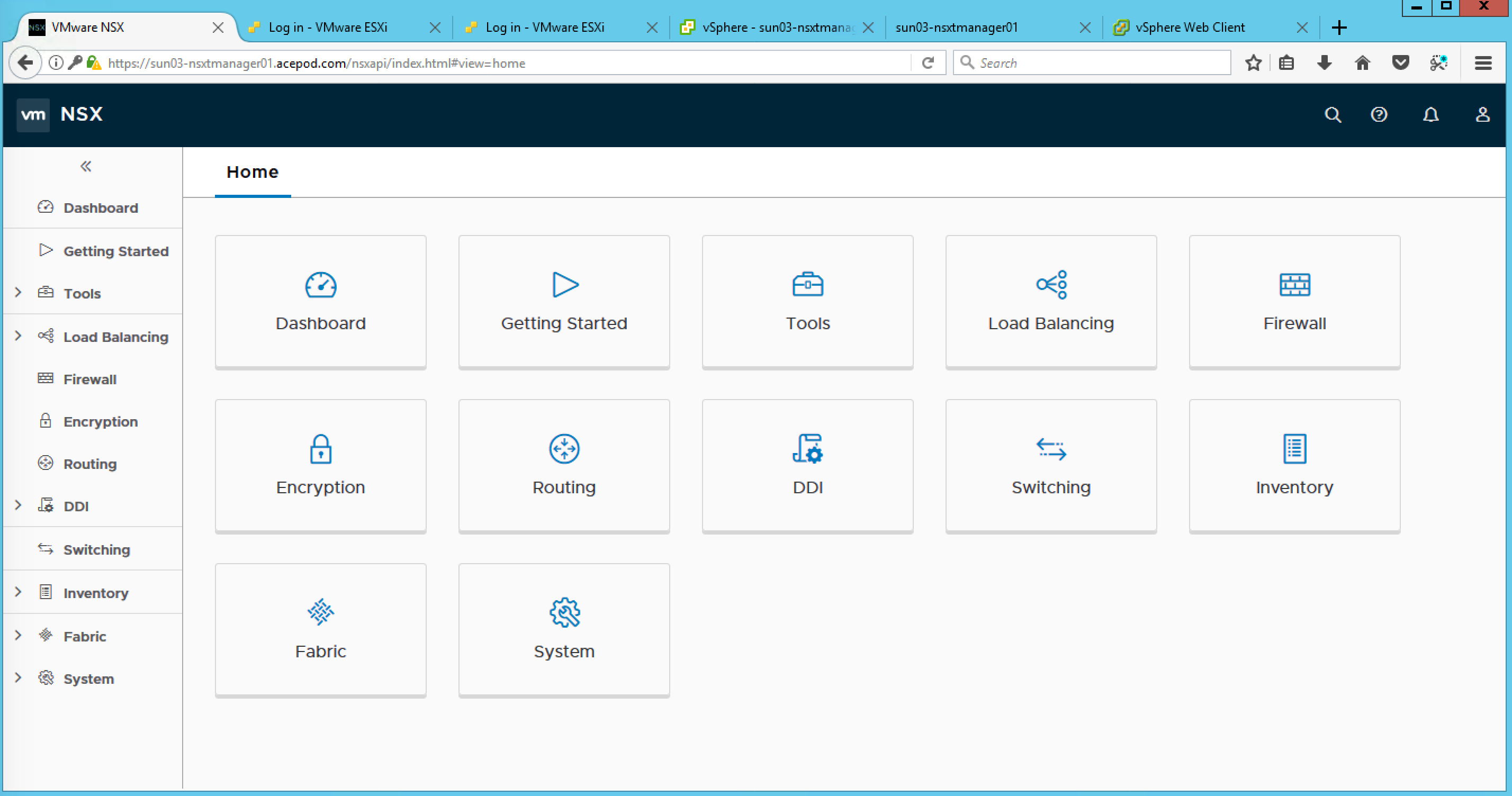
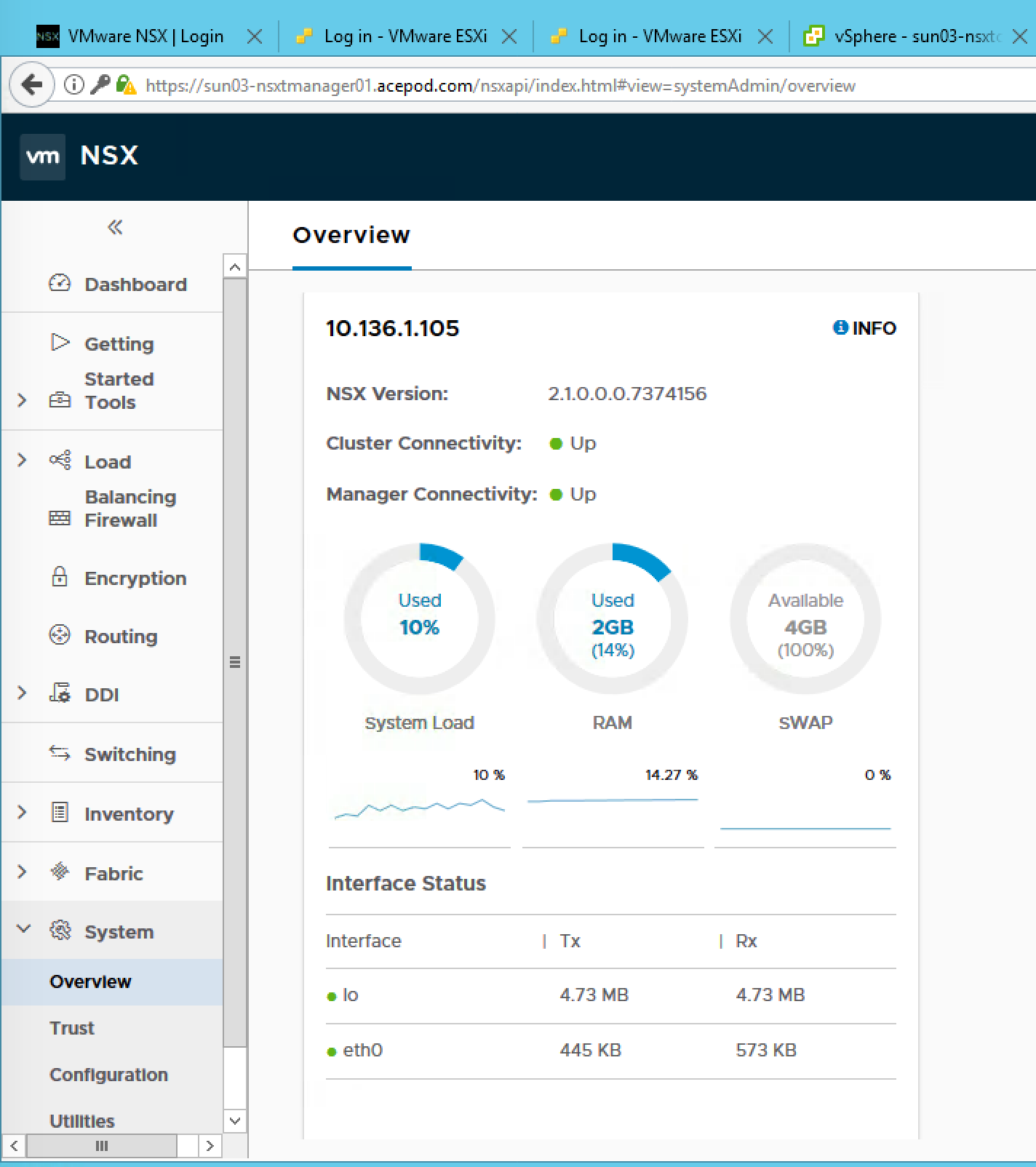
Finally able to login to the NSX Manager console.
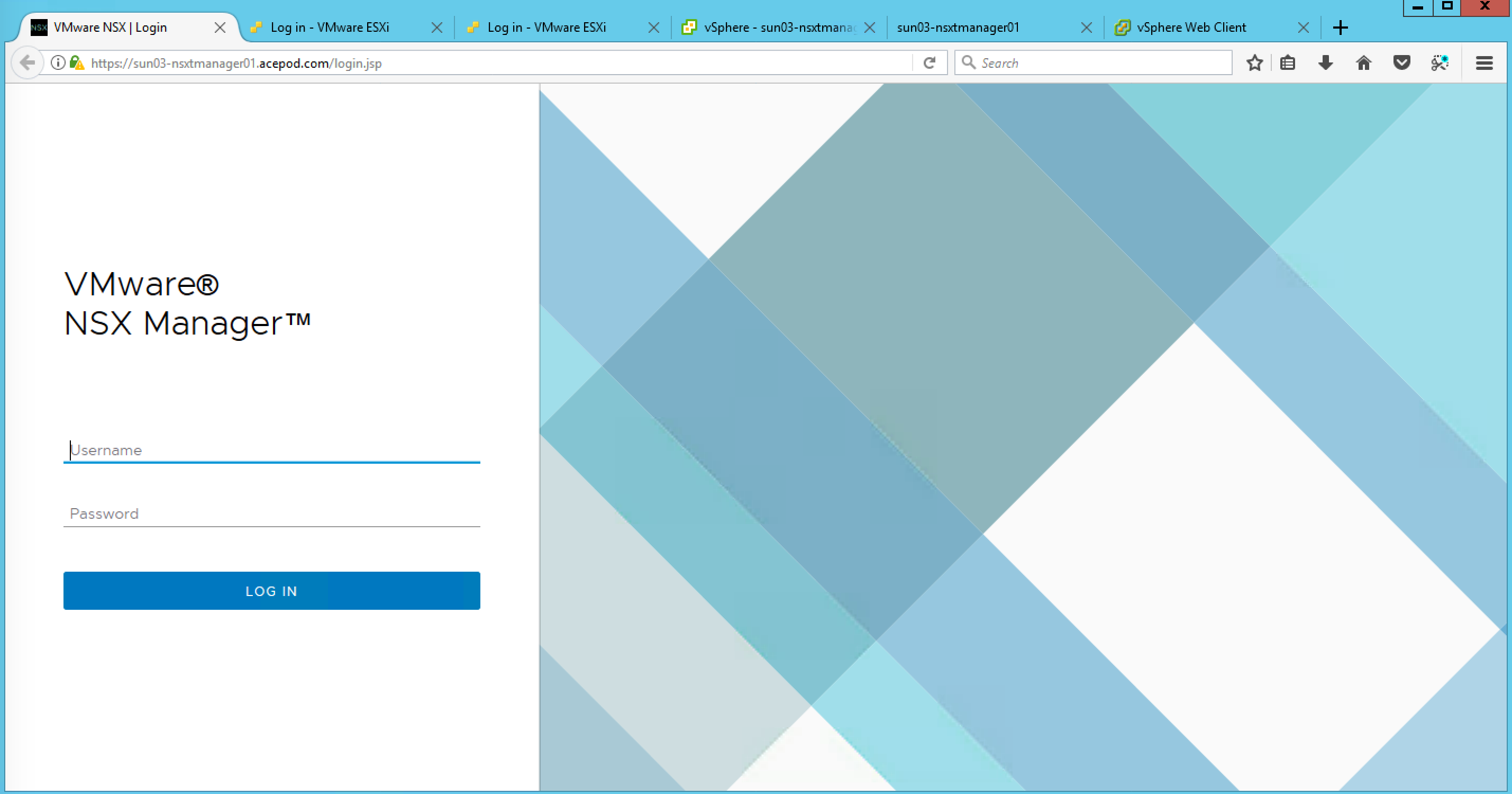
Trying to login to the web console of the NSX Manager.
Awesome! Able to login and dashboard is up!
Alright. so next will be the NSX-T Controllers.
Configuring the Controller Cluster
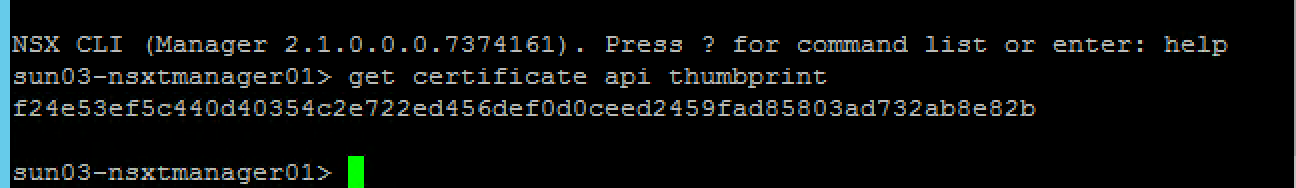
Retrieve the NSX Manager API thumbprint
- Log onto the NSX Manager via SSH using the admin credentials.
Use “_get certificate api thumbprint_” to retrieve the SSL certificate thumbprint. Copy the output to use in commands later
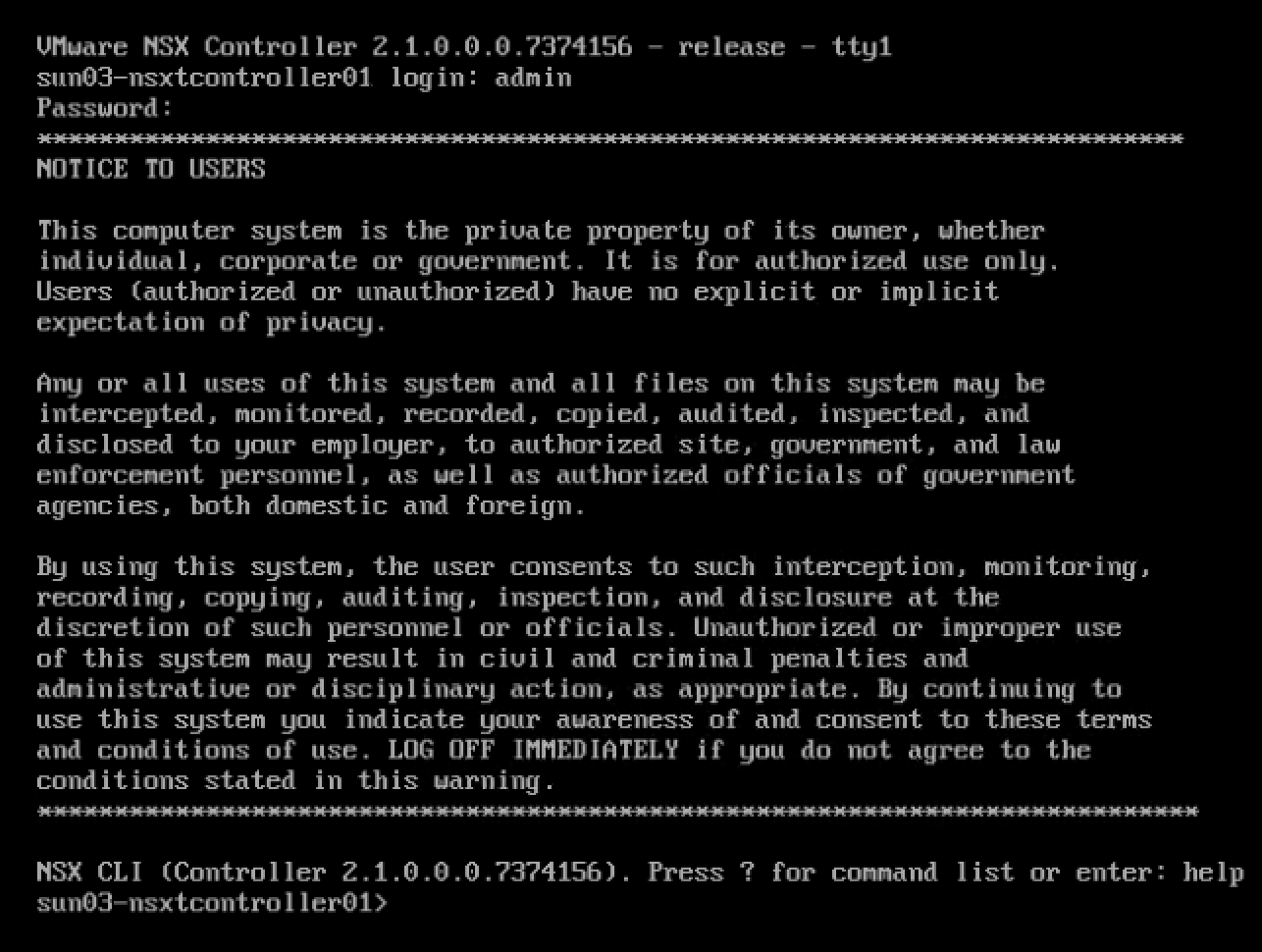
Join the NSX Controllers to the NSX Manager
- Log onto each of the NSX Controllers via SSH using the admin credentials.
- Use “join management-plane
username admin thumbprint 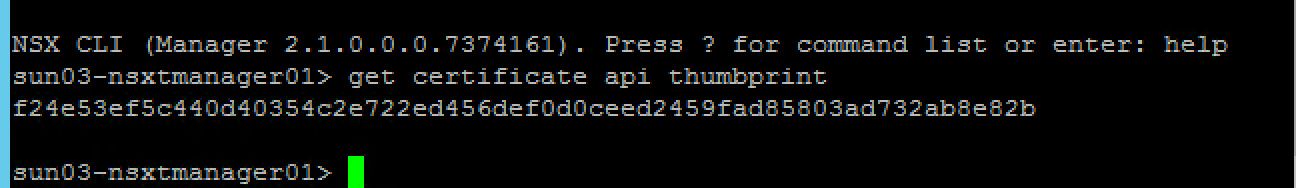
- Enter the admin password when prompted
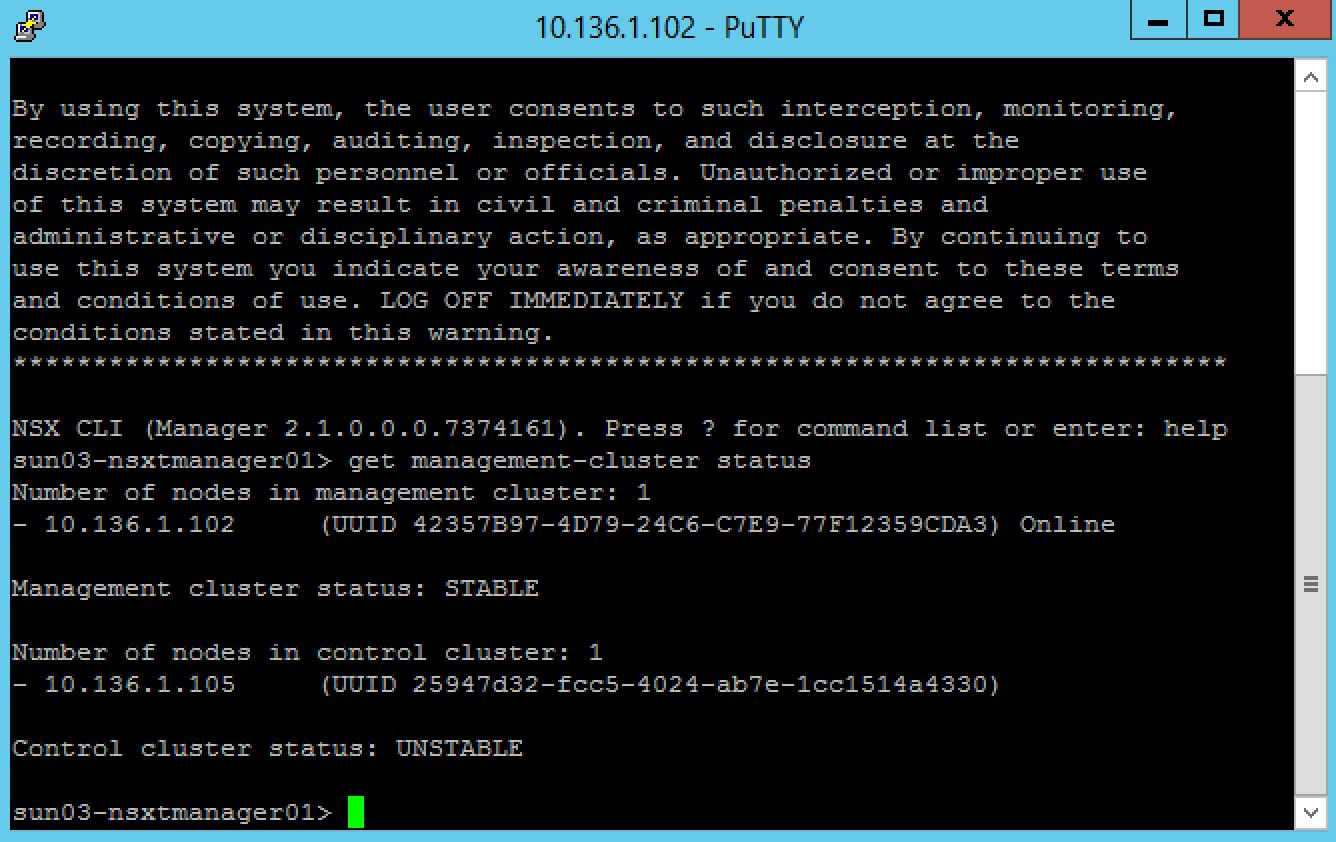
Validate the controller has joined the Manager with “_get managers_” – you should see a status of “Connected”
join management-plane 10.136.1.102 username admin thumbprint f24e53ef5c440d40354c2e722ed456def0d0ceed2459fad85803ad732ab8e82b
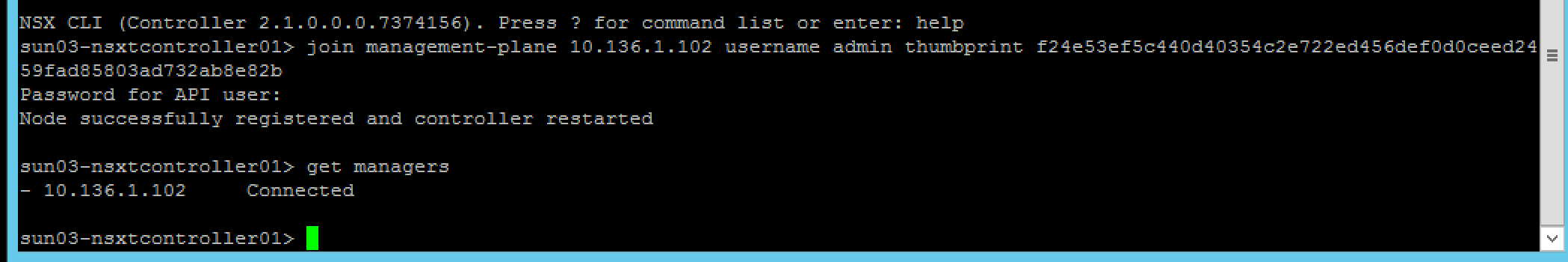
Repeat this procedure for all three controllers
Initialise the Controller Cluster
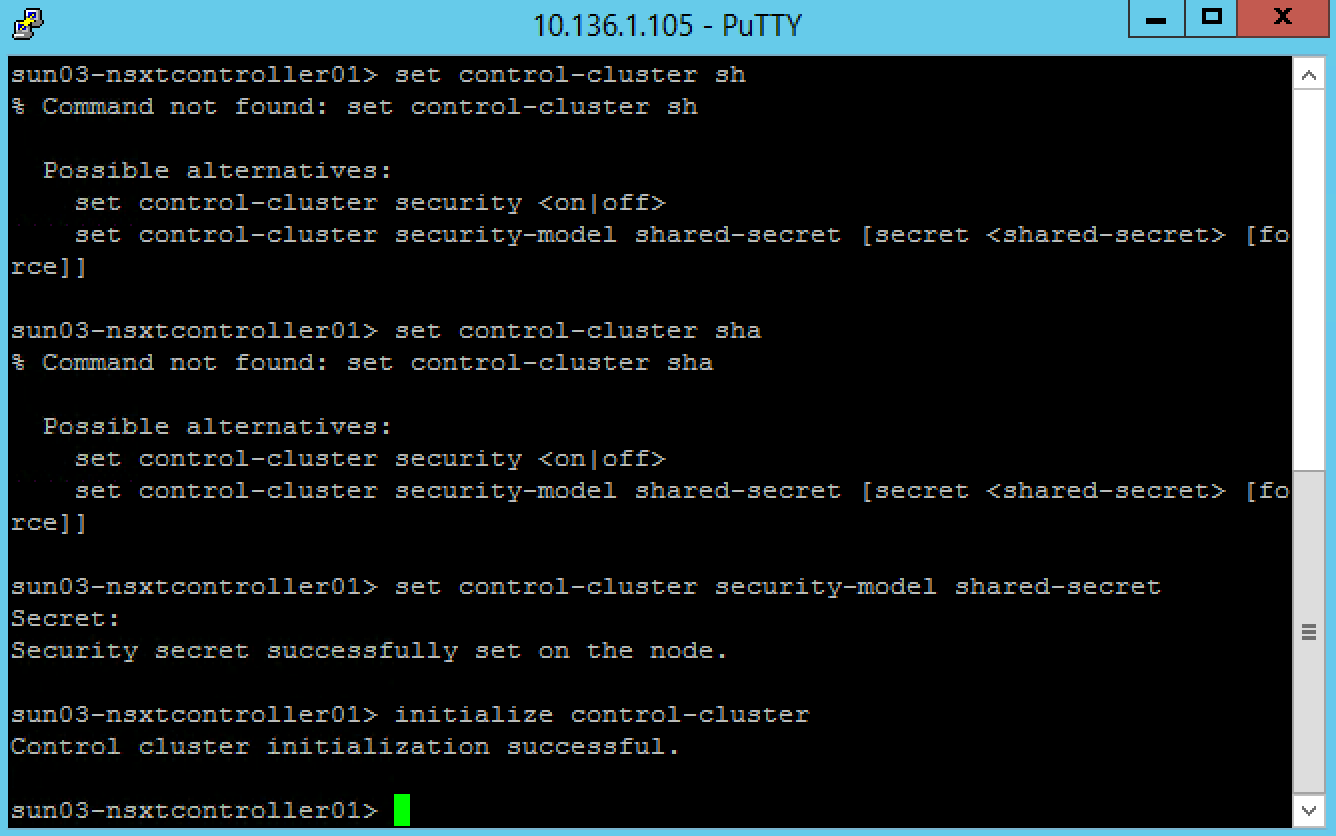
To configure the Controller cluster we need to log onto any of the Controllers and initialise the cluster. This can be any one of the Controllers, but it will make the controller the master node in the cluster. Initialising the cluster requires a shared secret to be used on each node.
- Log onto the Controller node via SSH using the admin credentials.
- Use “_set control-cluster security-model shared-secret_” to configure the shared secret
- When the secret is configured, use “_initialize control-cluster_” to promote this node:
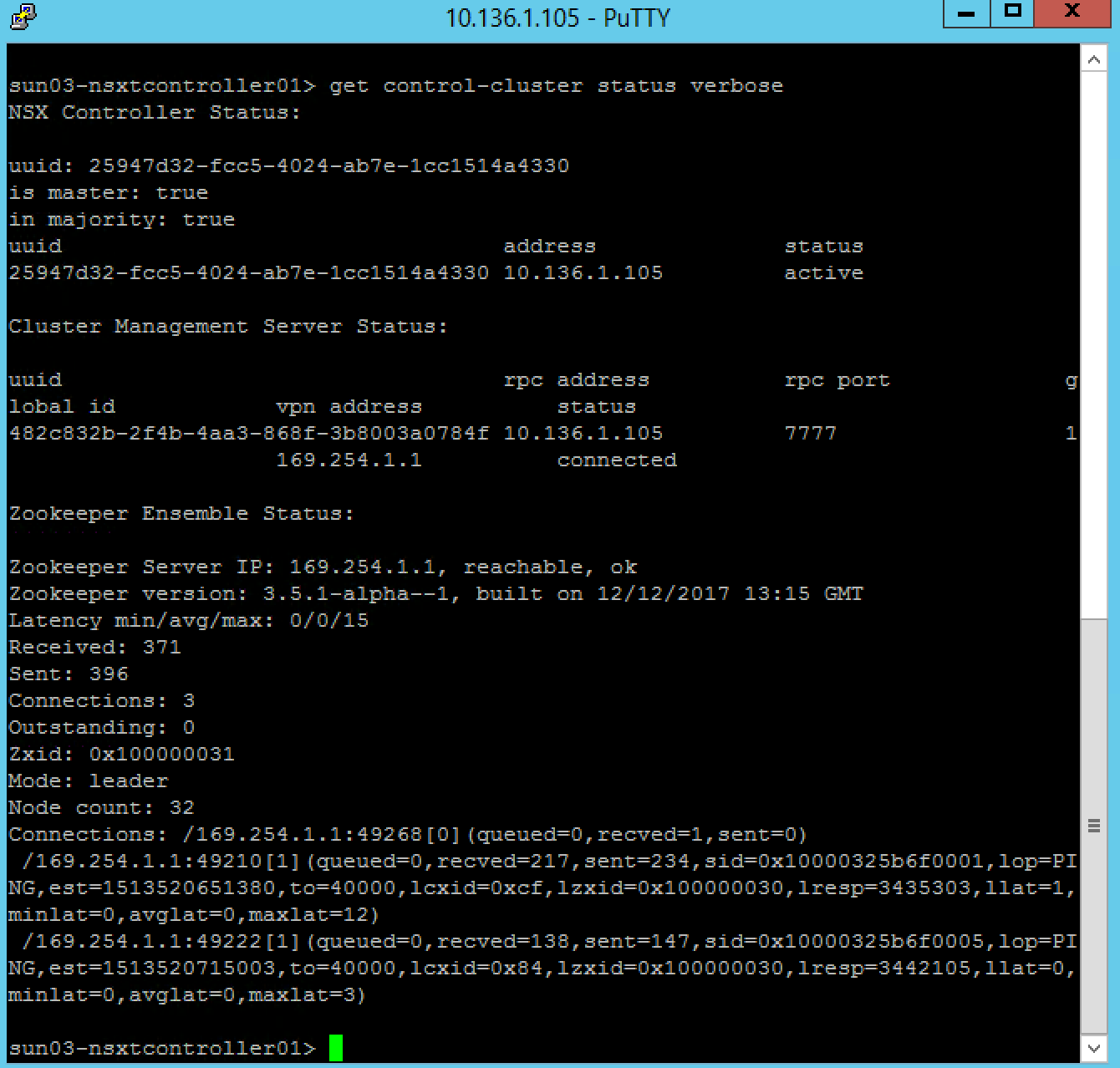
Validate the status of the node using the “get control-cluster status verbose” command. You can also check the status in the NSX Manager web interface. The command shows that the Controller is the master, in majority and can connect to the Zookeeper Server (a distributed configuration service)
Notice in the web interface that the node has a Cluster Status of “Up”
Preparing ESXi Hosts
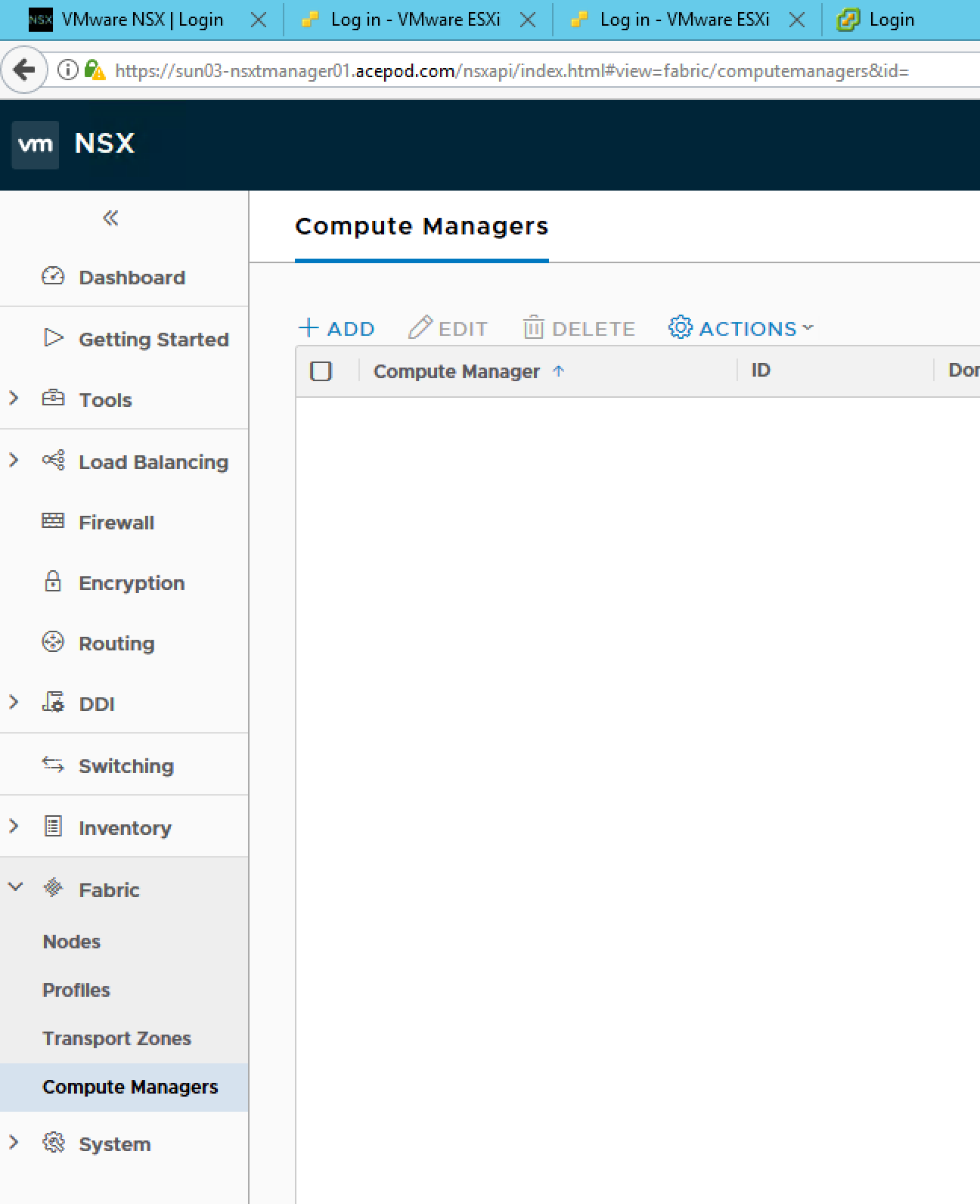
With ESXi hosts you can prepare them for NSX by using the “Compute Manager” construct to add a vCenter server, and then prepare the hosts automatically, or you can manually add the hosts. You can refer to Sam’s blog posts as he prepare the hosts manually for his learning exercise. Since my purpose is to quickly get the deployment up for PKS/PCF, Im going to use the automatic method using the “Compute Manager”
Login to NSX-T Manager.
Select Compute Managers.
Click on Add.
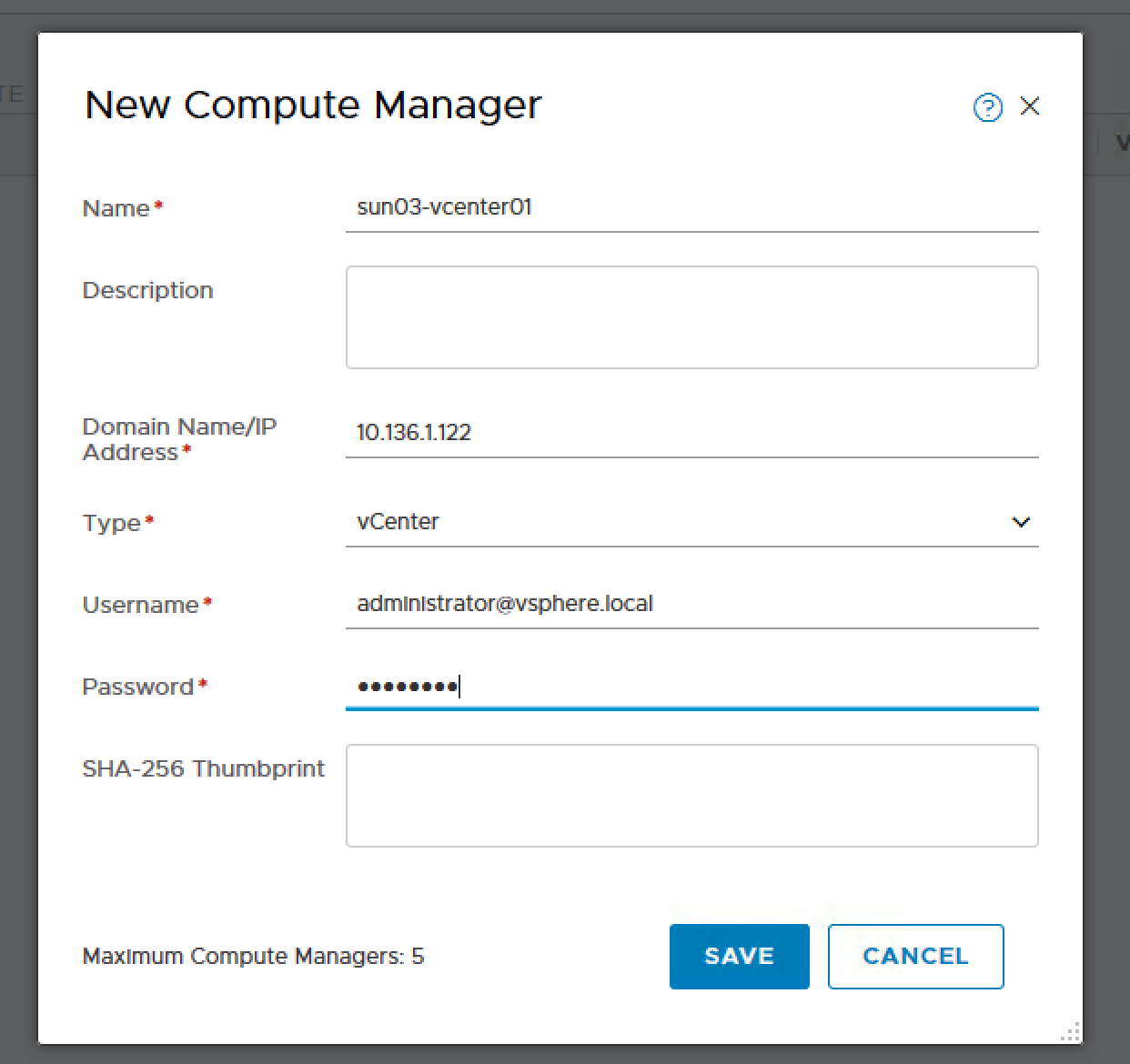
- Put in the details for the vcenter.
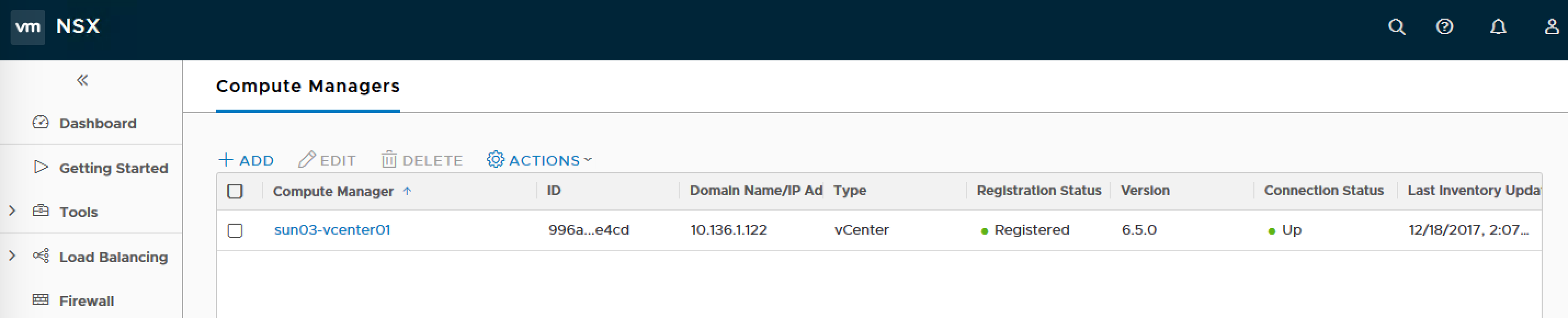
Success!
Go into Nodes under Fabric.
Change the Managed by from Standalone to the name of the compute manager you just specified.
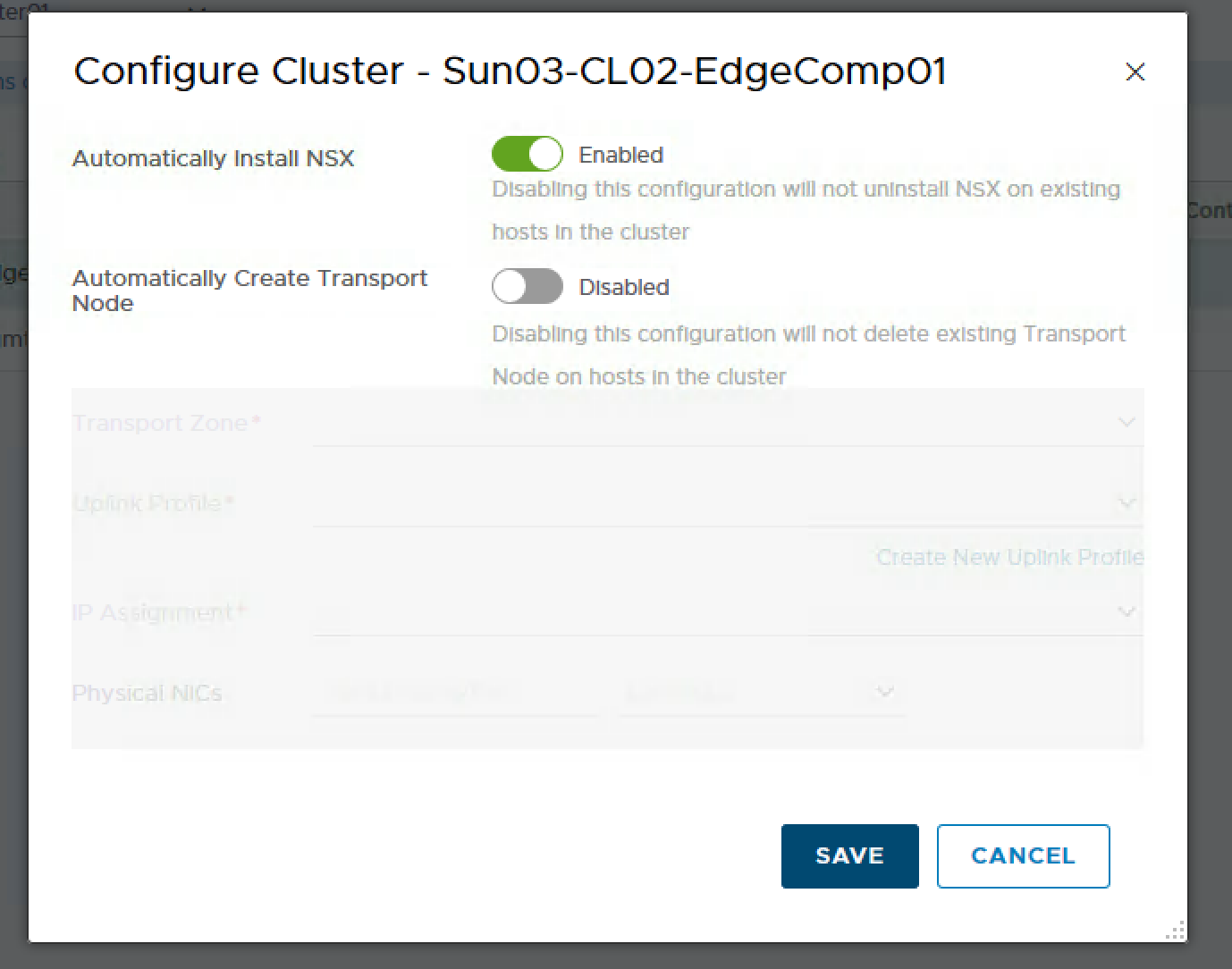
- Select the Cluster and click on Configure Cluster. Enabled “Automatically Install NSX” and leave “Automatically Create Transport Node” as Disabled as I have not create the Transport Zone.
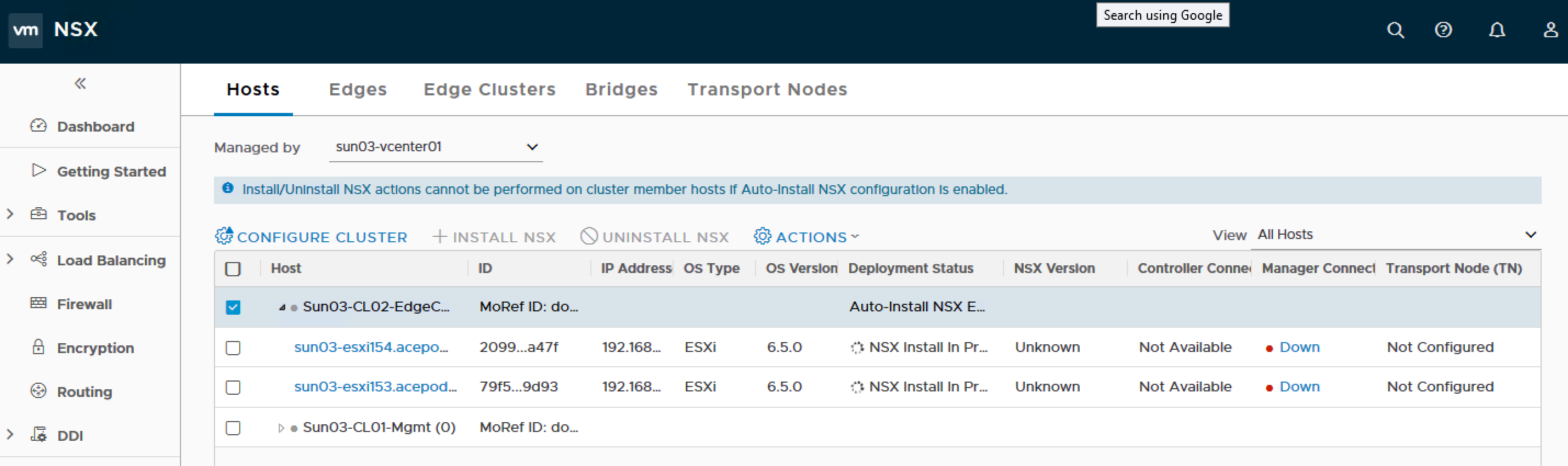
You will see NSX Install In Progress
Error! Host certificate not updated.
After some troubleshooting, I realize the host has multiple IP addresses, So what I did was to remove all of them except for the management IP address and the host preparation went on smoothly.
Host preparation was successful. As I was in the middle of writing this blog post, NSX-T 2.1 was just GA. Although the build number was pretty similar, I decided I will reinstall with the GA version. So much for the host preparation, I will uninstall and re-do everything again.
References